How to Protect Your Organization from Password Spraying
06 Dec 2021
Large-scale cyberattacks are not the only buzz in the cyber domain. Sometimes, the underlying attack tactics also make the news highlight. One such tactic that has gained much traction recently is password spraying.
What is Password Spraying?
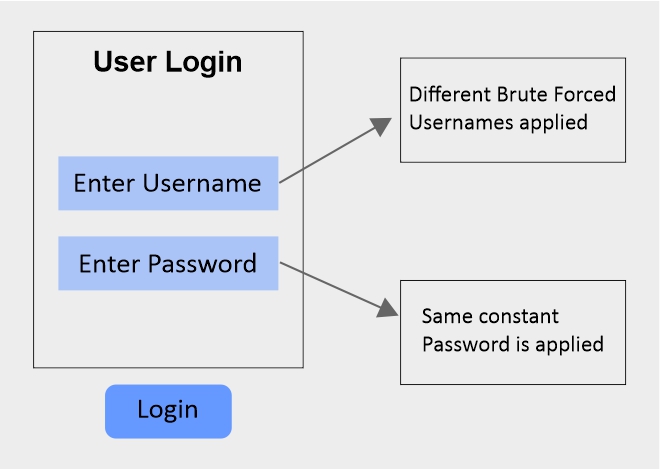
To target a single, high-value individual, hackers often have to spend more time doing spear phishing. But when they just seek to expand their foothold in the organization, low-level access is enough. This is when they try to target multiple company individuals while spending relatively less time on them. This technique of spending less time and targeting a huge volume to get credentials is called “Password Spraying.”
It falls under the category of Brute Force attack (T1110 MITRE ATT&CK). Through Password Spraying, the adversary tries to access systems by using either a single or a list of common passwords like “000000” or “012345” against a tremendous group of usernames. This helps to find valid credentials for some of those usernames. An outsider usually carries out this type of attack access credentials of any web confronting framework or cloud-based SaaS application. It can also be directed by an adversary who already has a foothold within the network and wants to expand the access.
Since the adversary attacks a large group of usernames in Password Spraying, it is said to be a high-volume tactic. It’s a robust sub-technique that malicious actors can use to gain legitimate credentials and compromise authentication mechanisms. The advantage to adversaries here is that this tactic, unlike other credential assaults such as brute force, enables them to move in the network unnoticed by avoiding account lockouts.
Scenario:
Since Password Spraying uses standard credentials, such attacks are common where default password keys are set and provided for all the new users by either the application itself or the system administrators.
Some of the commonly targeted IPs and services for Password Spraying includes:
- FTP (21/TCP)
- SSH (22/TCP)
- Telnet (23/TCP)
- HTTP/HTTP Management Services (80/TCP & 443/TCP)
- Kerberos (88/TCP)
- NetBIOS / SMB / Samba (139/TCP & 445/TCP)
- LDAP (389/TCP)
- MSSQL (1433/TCP)
- Oracle (1521/TCP)
- RDP / Terminal Services (3389/TCP)
- MySQL (3306/TCP)
- VNC (5900/TCP)
Besides SaaS applications, attackers can also target single SSO, VPN servers, and web-based email applications like O365.
Some common TTPs used for carrying out this attack include:
- Conducting online research and leveraging social engineering to identify target organizations and the user accounts within
- Using commonly and widely used passwords (e.g., “Password,” “Admin@123,” 123456, “qwerty”) to execute Password Spraying
- Accessing more email contacts through the compromised accounts to target them
- Exfiltrating data through lateral movement in the compromised network
Password Spraying Methods:
- Low and slow – Patience is the key to executing a successful attack. To run the most sophisticated attack, the threat actor will usually use multiple IP addresses and a small list of curated password guesses to attack numerous accounts simultaneously.
- Availability and reuse – Malicious threat actors can benefit from the large number of credentials uploaded on the dark web daily, also known as “credential stuffing.” With every new cyber breach going public, a new set of compromised credentials are uploaded, and adversaries can use these credentials to curate their password list quickly and begin executing the attack.
Impact:
If Password Spraying is executed successfully on an individual, the victim may lose sensitive information. On the other hand, if it is targeted at an organization, it can lead to disrupted operations, significant financial losses, and reputational damage.
Detection:
Although Password Spraying enables the threat actors to evade account lockouts, one can still detect this attack by closely monitoring authentication logs. While trying to attack a particular system or application, the adversary would have to try the common passwords across multiple accounts, leading to numerous authentication attempt failures. By monitoring such login failures in the network, Password Spraying can be detected.
Some of the event IDs to continuously monitor and check are:
- For Domain Controllers:
- “Audit Logon” (Success & Failure) for event ID 4625.
- “Audit Kerberos Authentication Service” (Success & Failure) for event ID 4771.
- For all systems: “Audit Logon” (Success & Failure) for event ID 4648.
Listed below are some activities that can alert about a possible Password Spraying incident, and monitoring them can help in detection:
- Look out for activities from anonymous and malicious IP addresses.
- Look out for activities from infrequent countries.
- Look out for activities from suspicious IP addresses.
Mitigations:
- Deploy a unique authentication tool that does not use passwords as the first authentication factor.
- Install and enable Two- or Multi-factor authentication, especially on externally facing services. This authentication technique requires users to provide multiple authentications, such as passwords, PINs, biometrics, or trusted devices.
- Mandate using strong passwords that abide by National Institute of Standards and Technology (NIST) guidelines. They must include a combination of small case letters, upper case letters, numbers, and special characters.
- All the applications that provide a default password should enforce changing it upon the first login.
- Set countermeasures like account lockouts after a decided number of failed login attempts to prevent easy guessing of credentials. If lockout cannot be set, try using CAPTCHA.
- Consider implementing password-based attack protection on not only the Password field but also the User field.
- Leverage most advanced Managed Detection and Response (MDR) services such as SharkStriker MDR which combines Machine Learning, Human Intelligence, and Security Automation to detect most advanced threats and respond them swiftly.
- Conduct regular and frequent user awareness training for all the employees. Include modules to help understand Password Spraying, the threat associated, and the prevention steps in training.
How can SharkStriker Services Help?
Our ORCA based MDR service can help in detecting and responding to password spraying attacks against Active Directory as well as other authentication services in real-time. Standing for Observe, Response, Compliance, and Awareness, ORCA-based services can enable continuous monitoring and centralized visibility for quick detection and real-time response.